1. Formulate the 3 x 3 game as a search problem, i.e. define the states, the moves, etc
1. Formulate the 3 x 3 game as a search problem, i.e. define the states, the moves, etc
2. Draw the state space that would be generated by the Breadth-First Search
initial state given in Table 2. You can stop when the first goal state is reached. Perform the
moves strictly in the following sequence: Up; Down; Left; Right. Do not create more than
one copy of any particular state, and identify the goal state.
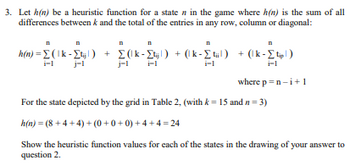
3rd question in second picture


Step by step
Solved in 3 steps

2. Draw the state space that would be generated by the Breadth-First Search
initial state given in Table 2. You can stop when the first goal state is reached. Perform the
moves strictly in the following sequence: Up; Down; Left; Right. Do not create more than
one copy of any particular state, and identify the goal state.



