number = int(input('Select number
Chapter2: Using Data
Section: Chapter Questions
Problem 17RQ: When you perform arithmetic operations with operands of different types, such as adding an int and a...
Related questions
Question
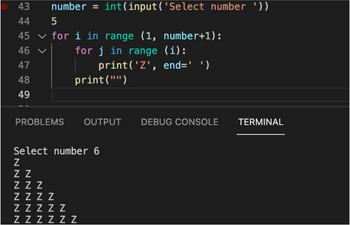
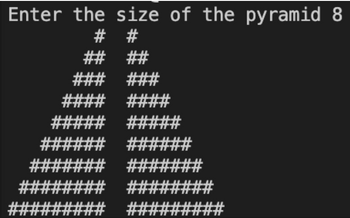
Use a similar python code to the first image, to make a double pyramid in the same form as teh second

Transcribed Image Text:● 43 number = int(input('Select number '))
44
5
45 ✓ for i in range (1, number+1):
46 ✓
for j in range (i):
47
48
49
print('Z', end=' ')
print("")
PROBLEMS OUTPUT DEBUG CONSOLE
Select number 6
Z
Z Z
ZZZ
ZZZZ
ZZZZZ
ZZZZZZ
TERMINAL

Transcribed Image Text:Enter the size of the pyramid 8
#
#
##
##
### ###
####
###
####
#####___#####
#######__#######
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
THIS CODE IS COMPLETELY DIFFERENT FROM WHAT I ASKED. I NEED A CODE THAT USES A LOOP LIKE WHATS IN THE FIRST IMAGE TO DO EXACTLY WHATS IN THE SECOND IMAGE. PLEASE I DONT WANT MY QUESTION WASTED AGAIN IM BEGGING
Transcribed Image Text:43
44
45
46
47
48
49
number = int(input('Select number '))
5
for i in range (1, number+1):
for j in range (i):
print('Z', end=' ')
print("")
PROBLEMS OUTPUT
Select number 6
Z
Z Z
ZZZ
ZZZZ
ZZZZZ
ZZZZZZ
DEBUG CONSOLE
TERMINAL
Transcribed Image Text:Enter the size of the pyramid 8
#
#
###
##
###
#### ####
##
#### ##
####
##
##
######
### ###
###
##
###
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage